COSMIC Introduction
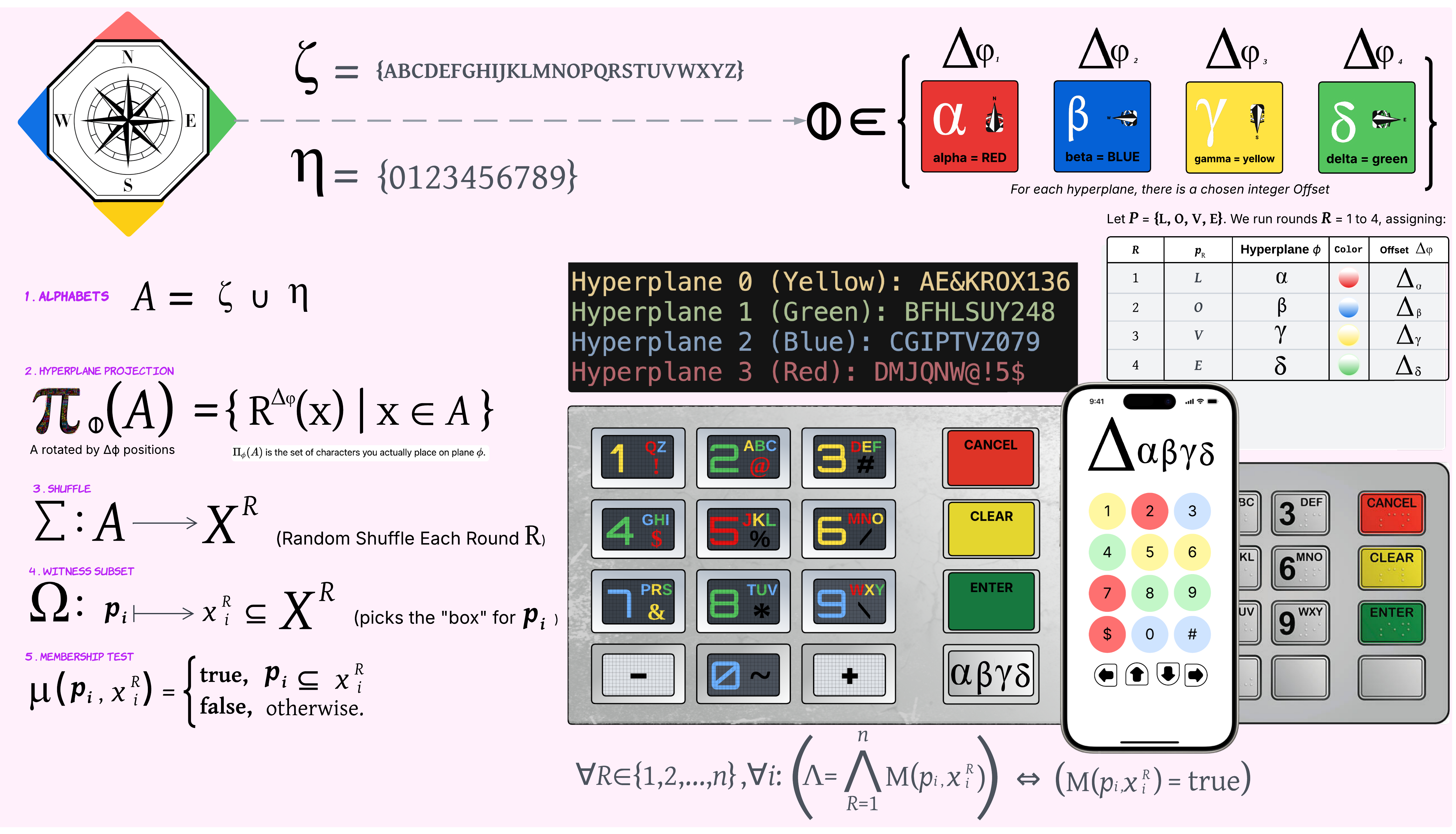
System Overview
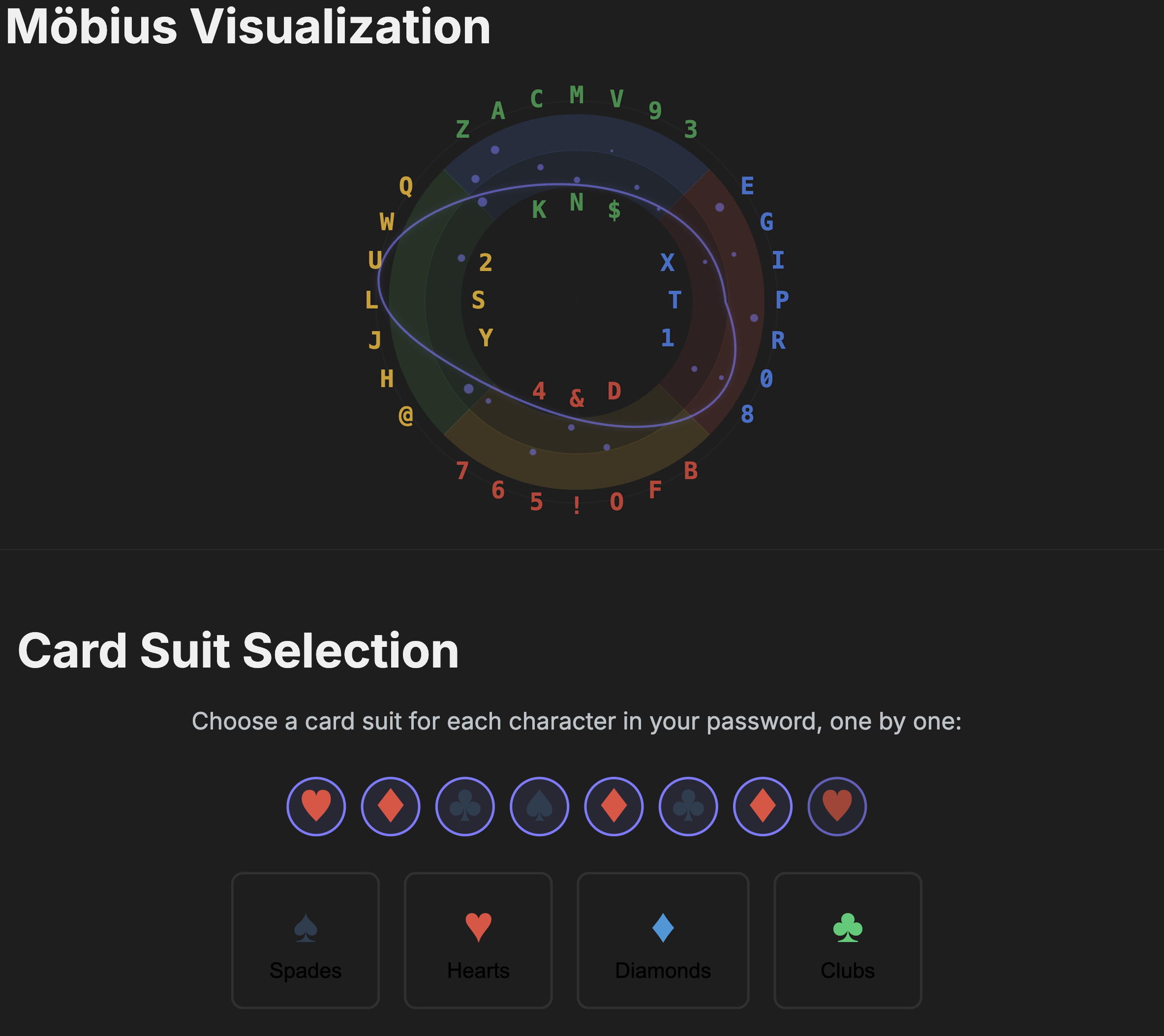
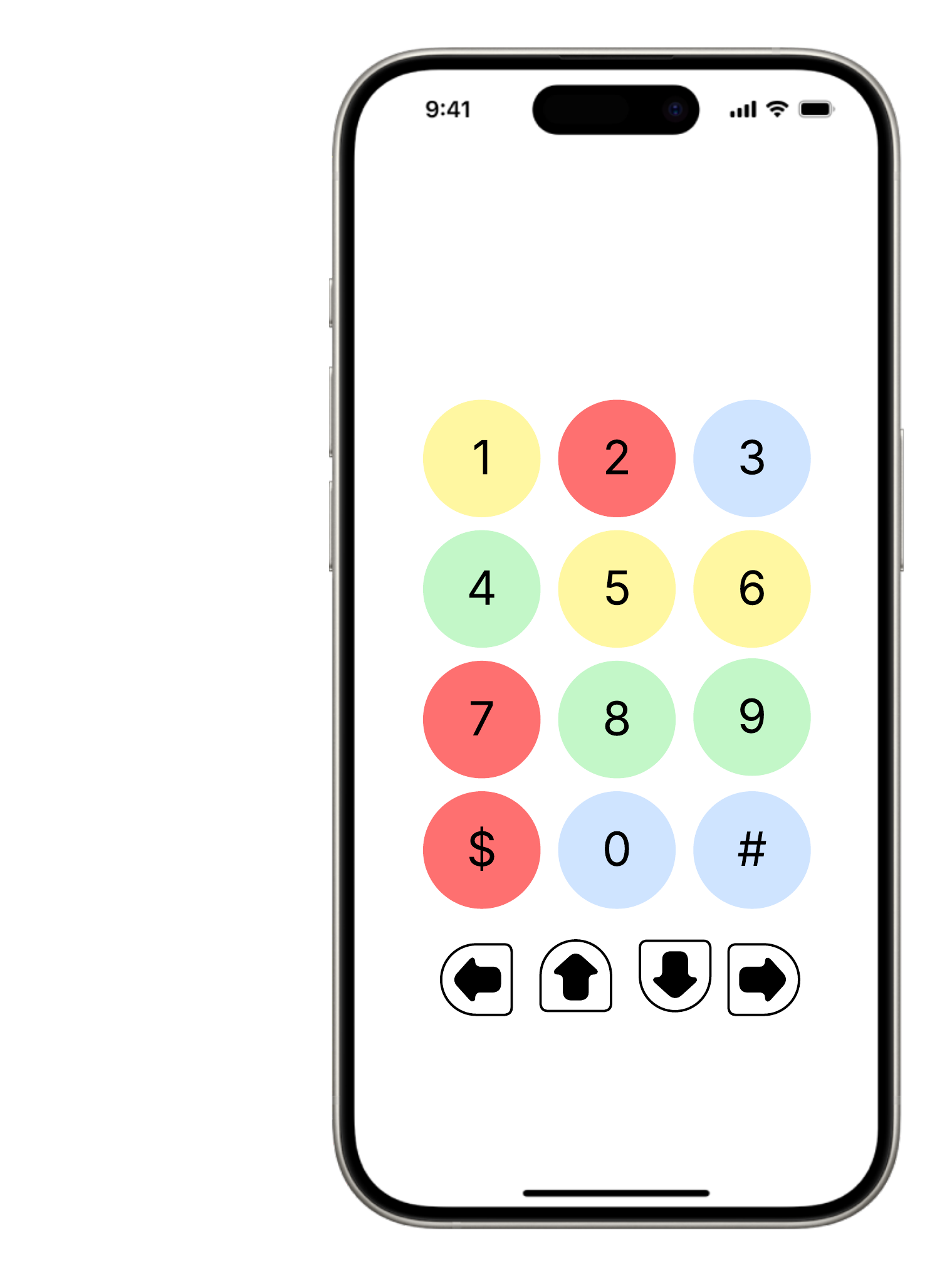
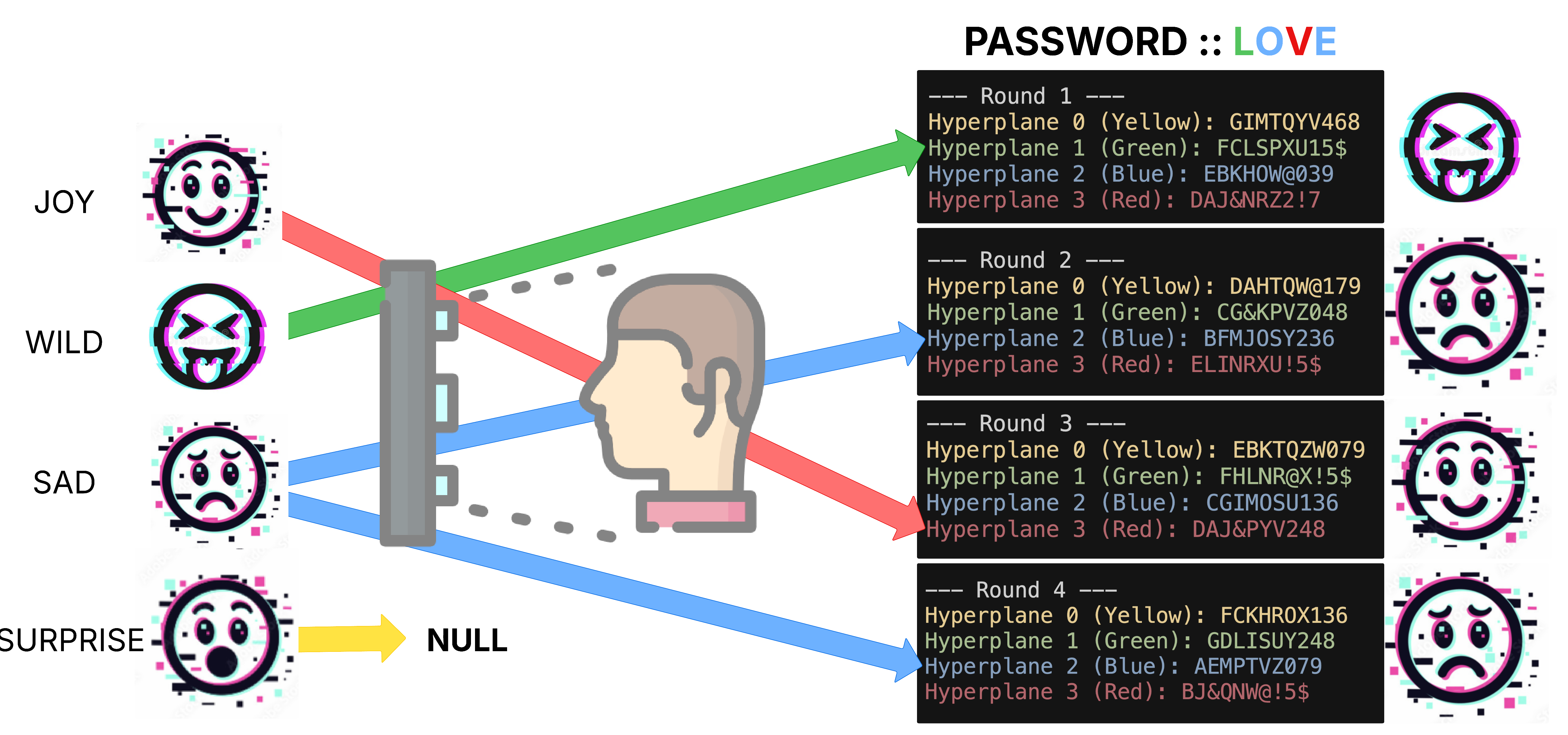
Cosmic turns password entry into an interactive visual experience. Users prove they know a secret by selecting images, colors, or symbols shown in a fresh random layout each time. Behind the scenes, zero-knowledge proofs confirm the user’s knowledge without revealing the secret itself.
- Random Session Seed → unpredictable puzzle every login.
- Visual Mapping → secret characters map to symbols via secure shuffling.
- User Selection → pick the right symbols; no text to steal or keylog.
- Proof-of-Knowledge → server validates choices, learns nothing else.
Benefits include resistance to phishing, key-logging, camera shoulder-surfing, and database leaks—while remaining user-friendly across web, mobile, kiosk, and IoT screens.
Cryptographic Core Components
1. Multi-Layered Randomness
- Combines hardware RNG, time entropy, server salt, and client noise.
- Multiple hash rounds scrub bias and expand to several dimensions.
- Guarantees high-grade unpredictability even if one source weakens.
2. Multi-Dimensional Symbol Mapping
- Characters shuffled across “visual planes” using non-linear math.
- Each plane binds to a symbol set (cards, arrows, emoji, etc.).
- Mapping differs every session—attackers can’t reuse observations.
3. Secure Prime Generator
- Generates large “safe” primes (p and 2p+1 both prime).
- Supports commitment scheme and long-term cryptographic strength.
4. Zero-Knowledge Loop
- User computes commitments in the browser (nothing secret leaves).
- Server issues a challenge; user responds; server verifies instantly.
- Outcome:
VALID/INVALIDwith zero leakage.
5. Authentication Chain
Random → Parameters → Symbol Mapping → User Selections → Commitments → Verification
6. Interactive Authentication Demo
Launch the terminal demo below to watch a full login cycle.
Advanced Protocol Details
- Dimensional entropy expansion yields a high-dimensional search space.
- Binding + hiding commitments prevent tamper & secret leakage.
- Merkle batching lowers proof size and verification time O(log n).
- Deterministic challenge derivation removes RNG bias while staying unpredictable.
- Optional non-interactive mode via Fiat–Shamir transform reduces round-trips.
Sample Verification Log
✓ Seed (256-bit).............. a8c0 6bb6 …
✓ Prime p (2048 bits)......... found
✓ Safe prime check............ passed
✓ 8 commitments generated
✓ Merkle root................. 83e7 c1bf …
✓ Challenge set {17,92,144} derived
✓ All responses verified...... ✔ VALID
Security Features
- Zero-knowledge property — no secrets in transit or at rest.
- One-time layouts defeat screen recording & replay.
- Time-bound tokens block delayed submission attacks.
- Uniform distribution foils statistical pattern mining.
- Side-channel mitigation — constant-time comparisons.
Protocol data flow
Note: For maximum protection, deploy Cosmic over TLS, enable server-side rate-limiting, and optionally add MFA for critical roles.
Post-Quantum Readiness
Cosmic’s core logic is algorithm-agnostic: you can swap in any post-quantum secure hash or signature scheme once standards finalise. Today we default to SHA-3 and classic ECDSA; tomorrow you can plug in Dilithium/Kyber without changing the user experience.
- 256-bit+ entropy budget withstands Grover attacks.
- Modular crypto layer isolates implementation specifics.
- Migration path documented in
/api/crypto-status.
Show Complexity Curve
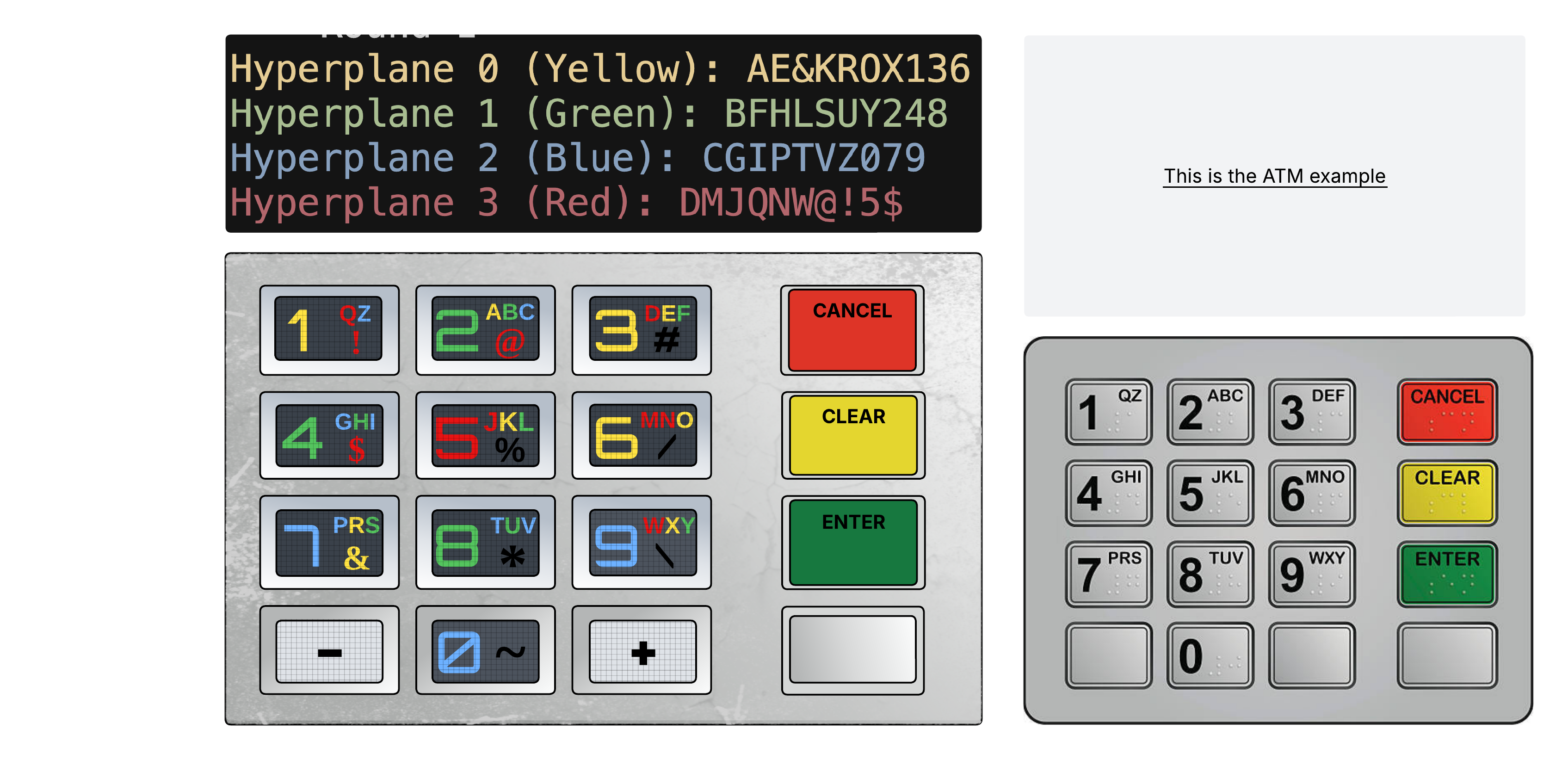
Implementation Examples
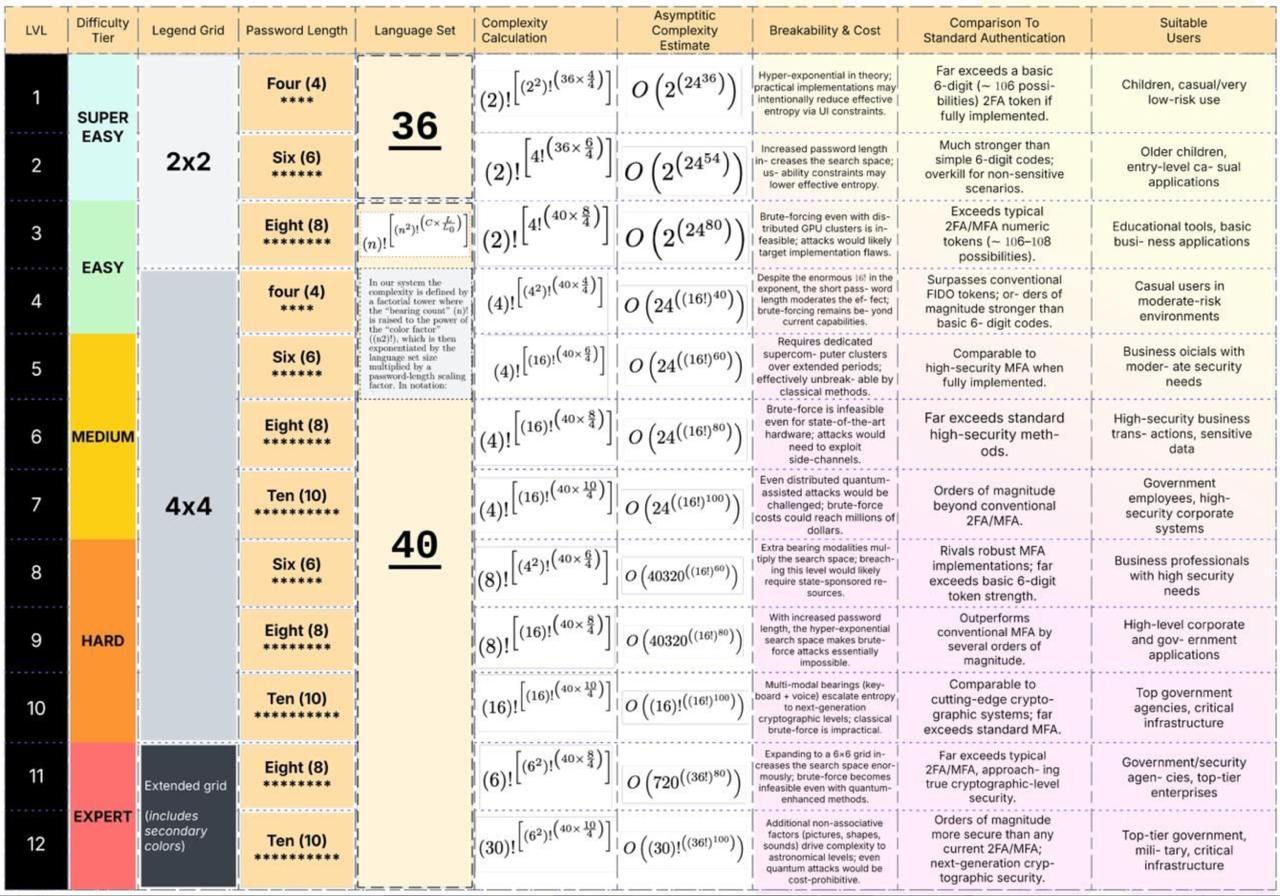
Cosmic can be skinned for any interface:
API Reference
Integrate Cosmic with just three core calls. The snippets below show cURL, Python requests, and JavaScript fetch.
curl -X GET "https://api.colorkey.ai/api/init-session" \
-H "Authorization: Bearer YOUR_API_KEY"curl -X GET "https://api.colorkey.ai/api/get-visualization\
?session_id=SESSION&selected_group=hearts" \
-H "Authorization: Bearer YOUR_API_KEY"curl -X POST "https://api.colorkey.ai/api/verify-colorkey" \
-H "Authorization: Bearer YOUR_API_KEY" \
-d '{
"session_id":"SESSION",
"selections":["hearts","spades","clubs","diamonds"]
}'Endpoint Summary
Creates a session — returns session_id,
password_length, timestamp.
Returns randomized symbol layout + animation data for that session.
Validates user selections; returns
{success,message,correct_count,total_count}.
Lists active hash algorithms & key sizes (for compliance).
Integration Guide
- Call
/init-session - Render UI from
/get-visualization - POST selections to
/verify-colorkey - Grant/deny access based on
success
Best practice: always use HTTPS, store API keys server-side, enable rate-limits, and monitor failed logins.